Sebagai pengguna internet aktif, saya selalu menggunakan VPN baik itu di HP, PC, koneksi selular, maupun WiFi (rumah dan kantor). Selain untuk peace of mind karena koneksi saya kontrol sendiri, VPN tersebut juga dikombinasikan dengan Pi-Hole DNS server untuk menghilangkan iklan jadi bisa browsing dengan nyaman dan ringan.
Cara menginstall Pi-Hole DNS server gampang banget, bisa dilihat langsung di websitenya. VPN menggunakan Wireguard atau OpenVPN, dengan tutorial di sini dan sini.
Nah ada kalanya karena alasan privasi, saya mau fully anonymous ketika berselancar, dengan cara tidak menggunakan public DNS resolver seperti Google, Cloudflare, dan OpenDNS. Client akan langsung mengirimkan query ke DNS root servers melalui recursive DNS server. Istilah kerennya sih, mencegah DNS leaking. Cuma ada satu kekurangannya, yaitu untuk domain yang baru pertama kali di-resolve, mungkin akan sedikit lebih lambat beberapa milliseconds karena path yang dituju lebih panjang.
Ada 2 aplikasi recursive yang populer, yaitu BIND dan Unbound. Di tutorial kali ini saya akan menggunakan Unbound, karena konfigurasi yang lebih sederhana dan resource usage yang lebih ringan.
apt install unbound
wget -O root.hints https://www.internic.net/domain/named.root
mv root.hints /var/lib/unbound/Konfigurasi Unbound:
/etc/unbound/unbound.conf.d/pi-hole.conf:
server:
# If no logfile is specified, syslog is used
# logfile: "/var/log/unbound/unbound.log"
verbosity: 0
port: 5353
do-ip4: yes
do-udp: yes
do-tcp: yes
# May be set to yes if you have IPv6 connectivity
do-ip6: no
# Use this only when you downloaded the list of primary root servers!
root-hints: "/var/lib/unbound/root.hints"
# Trust glue only if it is within the server's authority
harden-glue: yes
# Require DNSSEC data for trust-anchored zones, if such data is absent, the zone becomes BOGUS
harden-dnssec-stripped: yes
# Don't use Capitalization randomization as it known to cause DNSSEC issues sometimes
# see https://discourse.pi-hole.net/t/unbound-stubby-or-dnscrypt-proxy/9378 for further details
use-caps-for-id: no
# Reduce EDNS reassembly buffer size.
# Suggested by the unbound man page to reduce fragmentation reassembly problems
edns-buffer-size: 1472
# Perform prefetching of close to expired message cache entries
# This only applies to domains that have been frequently queried
prefetch: yes
# One thread should be sufficient, can be increased on beefy machines. In reality for most users running on small networks or on a single machine, it should be unnecessary to seek performance enhancement by increasing num-threads above 1.
num-threads: 1
# Ensure kernel buffer is large enough to not lose messages in traffic spikes
so-rcvbuf: 1m
# Ensure privacy of local IP ranges
private-address: 192.168.0.0/16
private-address: 169.254.0.0/16
private-address: 172.16.0.0/12
private-address: 10.0.0.0/8
private-address: fd00::/8
private-address: fe80::/10Jalankan Unbound setiap kali server boot:
systemctl enable unbound
systemctl restart unboundConfigure Pi-Hole
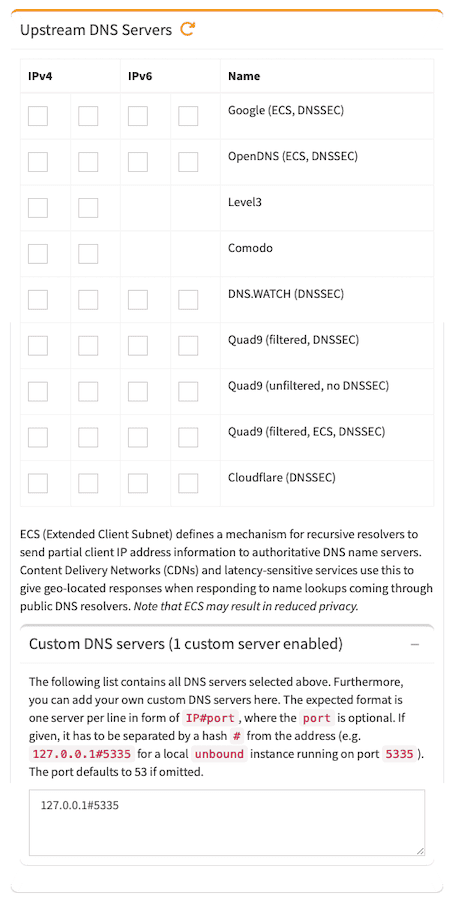
Selesai! Sekarang semua DNS queries akan langsung ke DNS root servers, bisa ditest dengan tools seperti dnsleak.com atau dnsleaktest.com, IP DNS server akan terbaca sama dengan IP address VPN server.
Bisa buatin gk mas recursive dns nya?
Tinggal ikuti langkah2 di atas harusnya udah bisa mas. Coba aja, kalau ada error paste di sini nanti dibantu.